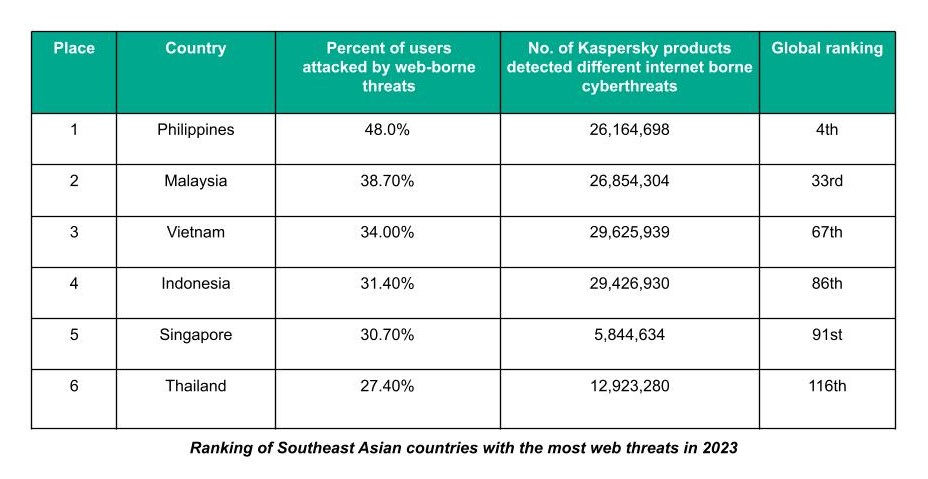
In 2023, Web threats targeting the Philippines were about two percent less (48%) than in 2022 (49.8%), according to the latest Kaspersky Security Network (KSN) report.
In the recent global ranking, the Philippines came behind Mongolia (51.8%), Moldova (48.9%) and Greece (48.8%). Since 2019, the country has consistently been in the top 10 ranking countries.
With this new data, the country moved two spots down to fourth place worldwide among countries most targeted by malicious files from the internet and phishing websites. It looks like a positive development but Kaspersky said it is strongly advising against dropping the armor.
“There are two things that could explain the drop in Web threats, albeit slightly. First is that we see the country is slowly making headway in cybersecurity. We classify the Philippines to be in the intermediate group of countries that are identifying cyberattacks and making efforts to implement rules,” said Yeo Siang Tiong, general manager for Southeast Asia at Kaspersky.
“The second one and this we have to seriously take note, is that cybercriminals are continuously taking other attack routes that might be off the radar. One trend that we consistently have been seeing lately is their preference for targeted attacks instead of the spray and pray method.”
Yeo added: “Complacency, however, is still not an option. Cybercriminals continue to develop their tools and techniques. They actually surprise cybersecurity experts all the time. Our mindset should be how to be able to hunt threats before they could cause harm and damage. At this point, I recommend that we should be talking more about threats as we proactively learn to detect and respond to them. This is where threat intelligence comes in handy.”
The Philippines, however, still topped the ranking in Southeast Asia, with the country logging the most attacks in the region with 48% of Kaspersky users attacked by Web-borne threats.
Kaspersky explained that Web or online threats are attacks through browsers which are also cybercriminals’ tried and tested way to spread malware. It can easily be done with or without the involvement of the victim, it noted.
Meanwhile, a Web attack with victim participation is done through social engineering. The victim is tricked into doing something that jeopardizes their personal security or the security of the organization they work for.
The objective is to get the victim to respond by clicking an infected email attachment, a compromised website, or responding to a fake unsubscribe notice, among others.
Last year’s data breaches involving a government agency and an e-wallet company, which were each reportedly traced to phishing, are examples of this type of Web threat.
“An attack requiring no victim involvement is through drive-by downloads. By simply visiting a compromised website, their device gets infected automatically (and silently) particularly if they failed to apply a security update to one of their apps. This method is used in most Web attacks,” it said.



